Security as a Service (SECaaS)
Secure your business data and operations by outsourcing your cybersecurity.

Employing an in-house SOC team can be expensive and time-consuming, especially for a small or medium sized business. Instead, you can employ a Security as a Service provider to manage the daily running of your cyber security posture. This can be tailored towards your specific needs and easily scales as your business grows.
What does SECaaS do?
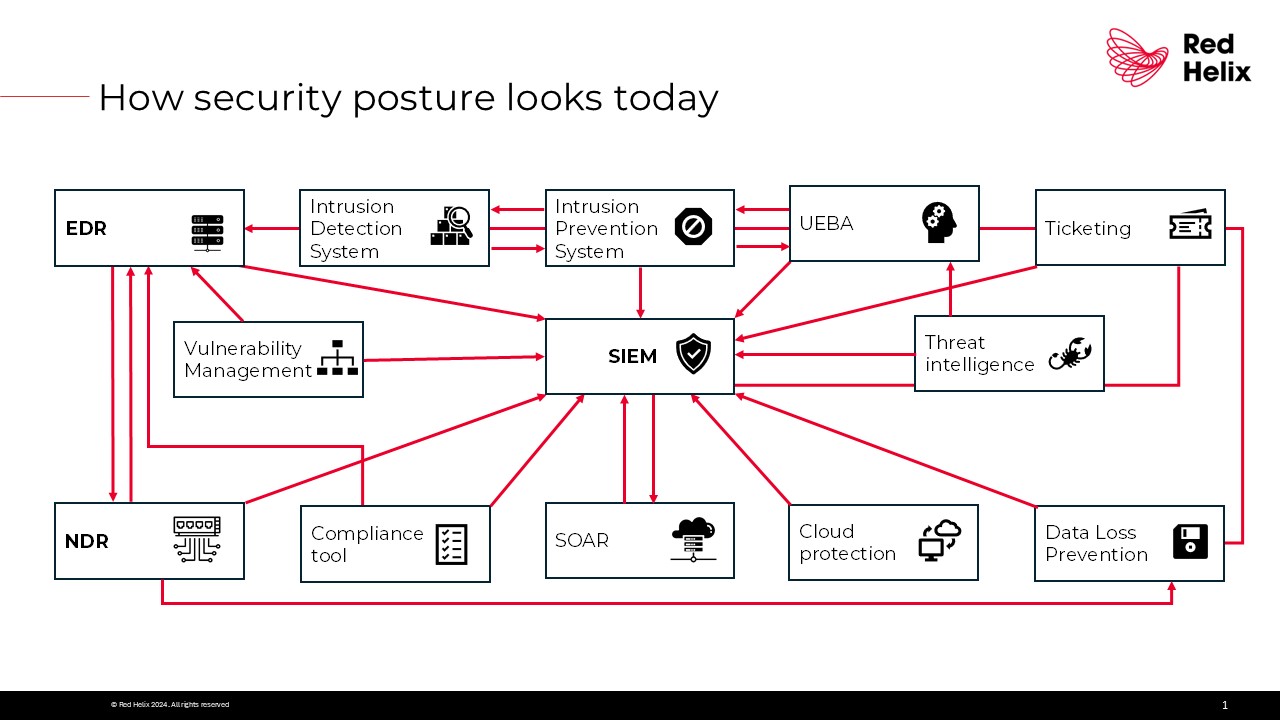
A SECaaS provider manages and monitors your organisation’s security systems remotely. This is run on a subscription basis and usually hosted by cloud providers. This model is becoming ever-more popular for businesses as an alternative to in-house IT security teams. Security as a service usually works in an overarching manner. It provides a centralised system whereby all your required security measures are managed in one place, by one SECaaS provider.
Examples of SECaaS
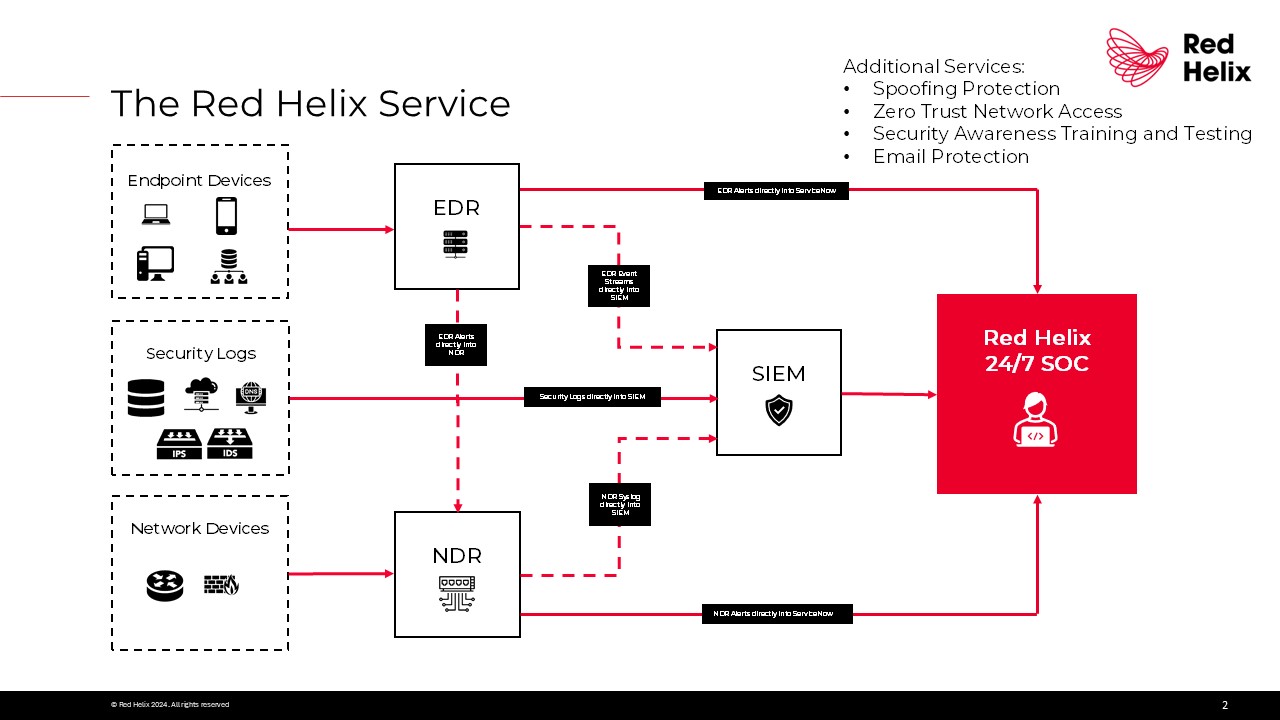
- Managed Detection & Response (MDR)
- Security Information & Event Management (SIEM)
- Network Detection & Response (NDR)
- Endpoint Detection & Response (EDR)
- Vulnerability scanning
- Intrusion detection
- Email protection
- Spoofing protection
- Zero Trust Network Access (ZTNA)
- Network security
- Antivirus Management
- Spam Filtering
- Identity and Access Management (IAM)
- Intrusion Protection
- Continuous monitoring

Current threats in the cyber landscape range from ransomware, generative AI, to phishing scams, and every day we are faced with new and emerging cyber security challenges. It is tiresome and costly for internal IT teams to constantly keep up-to-date with these. Alongside this, the technology landscape is overwhelming, as new vendors and solutions struggle to enter the already oversaturated market. As a customer, it is difficult to navigate, and many suffer from choice-fatigue. Traditional security solutions are expensive, fragmented and siloed. Legacy systems are struggling to keep up-to-date, leading to visibility gaps, and the high number of false positives means that IT teams are being distracted by repetitive and menial tasks. This has led to reduced business efficiency.
Cyber Insurance and Supply chain security
As compliance expectations rise, cyber insurance costs are projected to increase, with insurers requiring proof of strong cyber security practices. The Cybersecurity Maturity Model Certification (CMMC) 2.0, for example, requires contractors to meet stringent standards, pushing businesses large and small to strengthen their security measures
Cyber insurance has become a critical tool for businesses to enhance their financial resilience and recovery against cyber incidents. However, obtaining coverage is becoming increasingly challenging due to the evolving cyber threat landscape. Insurers are tightening their requirements, making policies more expensive and selective. Therefore, you must have adequate understanding of the requirements necessary to comply with your cyber insurance policies.
To meet eligibility, businesses must implement robust security protocols, including access controls, monitoring, and supply chain security. Insurers are likely to focus on past cyber incidents and how they were managed, meaning organisations must maintain detailed records of previous breaches. This is often difficult for organsiations to keep up-to-date with. Therefore, SECaaS can help you to comply with your cyber insurance policy and even achieve a reduction in your premium by reducing the likelihood and impact of a breach.
Strengthening supply chain security is also becoming more critical, especially in regulated industries. Proactive preparation, including regular audits and compliance checks, will not only help companies secure insurance but also reduce their overall cyber risk. As the supplier selection process matures, more companies will make cyber security measures mandatory. It is important that your supply chain is sufficiently prepared, or you may lose out on potential customer/vendor relationships. This is already prevalent in the financial sector and is fast becoming the norm across all industries as cyber is increasingly recognised for the value it adds to organisations winning new contracts.
SECaaS will support you in meeting the basic privacy requirements of wide-ranging regulations such as the Data Protection Act or GDPR. These require businesses to safeguard personal data with responsible access controls and breach detection. SECaaS will support you in meeting the basic privacy requirements of wide-ranging regulations such as the Data Protection Act or GDPR. These require businesses to safeguard personal data with responsible access controls and breach detection.
Calculating the cost of an internal Security Operations Centre (SOC)
A fully staffed SOC typically requires security analysts, engineers, managers, and incident responders to cover shifts 24/7. Salaries rise sharply from recent graduates earning £45,000 up to £100,000 per year for managers. You should also allow an additional 10-20% to account for round-the-clock staffing. For a small to mid-sized SOC, you may need at least 6 staff to cover 24/7 operations. Finally, you need to allow for training and certification costs.
On top of this, would must individually acquire the technology to protect your infrastructure. This includes but is not limited to Endpoint Detection and Response (EDR), Network Detection and response (NDR), and Security Information and Event Management (SIEM). Technology costs vary hugely depending on users, data ingest and tools. They can range from: £50,000 – £600,000 annually. This does not consider the physical infrastructure which needs to be built for an on-premise SOC such as the hardware, and back up.
Overall, you should expect to invest at least £1,000,000 to set up a complete 24/7 SOC.
Our Solution
At Red Helix, we advocate for 24/7 threat detection and response. Cyber Security as a Service, establishes visibility across your IT infrastructure to detect anomalous activity, contain threats and respond appropriately. It also safeguards your valuable data. Outsourcing allows the benefits of expert advice and innovative use of technology, gaining access to high-level security at a fraction of the cost. You do not have to worry about securing comprehensive cyber insurance as SECaaS covers all bases, therefore reassuring boards and protecting every link in the supply chain.